Secure Your VPN: How to Protect Company Data from Cyberattacks on VPNs
Introduction
For many years, VPNs have been considered effective tools for secure remote access to company resources. Their popularity is growing as more users work remotely or in hybrid models.
However, the end of 2023 and the beginning of 2024 brought disturbing reports of vulnerabilities in VPNs widely used by corporations and organizations worldwide. Even the US government responded. Users have realized that VPNs are not free from threats, mainly due to the need to log in to the VPN server. Credentials and the identity verification process are common attack vectors for criminals.
However, this process can be additionally secured. How can it be done effectively? How can VPN security be quickly and comprehensively strengthened?
In this e-book, we have collected important information about VPNs, their vulnerabilities, and how to protect these tools against cyberattacks.
We invite you to read it.
VPN, providing secure remote access to company systems
(in theory)
What is a VPN?
A VPN, or Virtual Private Network, is a service that protects your internet connection and online privacy. It works by creating an encrypted tunnel between your device and the VPN server, enabling secure access to company resources for people outside the company's headquarters and internal network. A VPN tunnel can also connect company offices in different locations, both domestically and internationally.
VPNs are especially important for companies with many applications and a significant amount of data stored in internal data centers, as employees need secure access to these resources.
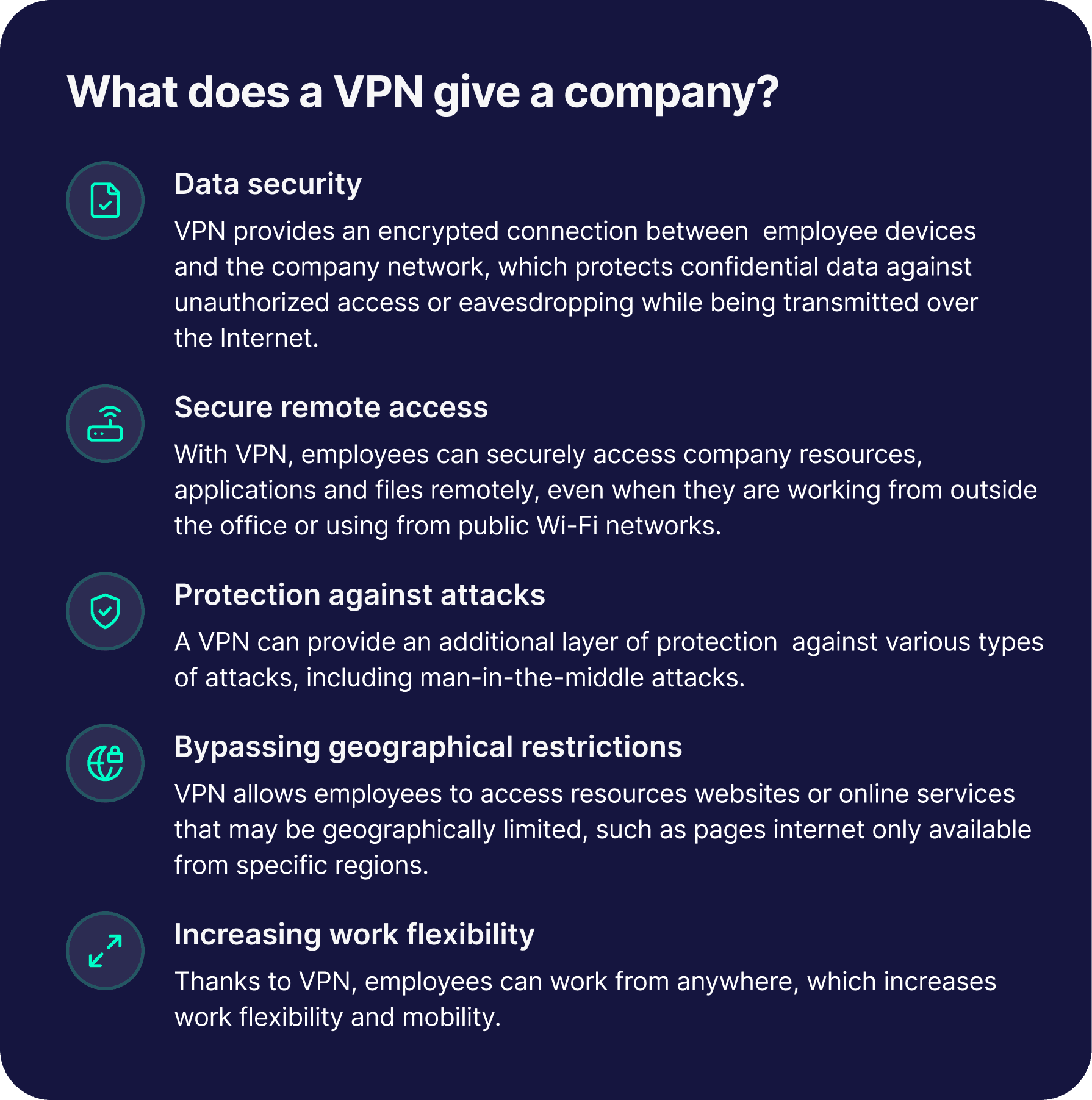
Benefits of using VPNs in companies
Using a VPN in a company can bring several benefits related to security on one hand, and work comfort and flexibility on the other.
Ways to implement VPNs
Enterprises today can use two different ways to implement VPNs: full VPN and split VPN. The former secures all network traffic. In other words, all the network traffic of an employee who connected to such a VPN goes through the company. The advantage of this solution is greater data security, the disadvantage is the lower work comfort with lower VPN performance
and slower data flow, and the need to build a powerful infrastructure
that can handle all traffic from all users.
Split VPN only encrypts part of the traffic from your device. At the configuration stage, the company can specify which connections
and applications should use VPN and which should not. This makes the traffic faster and smoother, but also less secure, because the company is unable to block potentially threatening websites or services used by the employee.
Remote access VPNs
VPNs can also be divided into private, site to site and remote access VPNs, or - colloquially speaking - VPN tunnels. The main purpose of the latter is to enable an employee or user to remotely access company resources.
Such solutions are often used by companies that practice remote or hybrid work. A VPN tunnel allows employees to use applications, data or files in the same way as when they are in the company's internal network. A VPN gives users flexibility and mobility while giving the company control over their behavior.
SSL VPN and IPSec VPN
SSL VPN and IPSec VPN are two solutions that protect network connections, but they differ in their applications and functions. IPSec VPN operates at the network level (layer 3 in the ISO/OSI model), encrypting all network traffic between two points. Requires configuration at the device operating system level. It can provide secure remote access to the entire company network. It allows employees to use network resources from anywhere.
On the other hand, SSL VPN works up to the application layer level (layer 7 in the ISO/OSI model). It can encrypt traffic to specific applications or services using a web browser. Authentication in such a tunnel is often done via a website. This solution works best when accessing specific applications or network services, e.g. e-mail or CRM. Encrypting only selected traffic has a positive impact on the performance of the solution itself, although the lower level of security of the solution itself should be recognized due to working on higher layers of the ISO/OSI model.
VPN security problems
VPN vulnerabilities
While VPNs are intended to keep organizations, users, and data safe, they are also vulnerable to threats in their own right. In the case of remote access VPNs, cybercriminals can attack two entry points. The first is the user. A tunnel begins on a website or app with a VPN server login form. The second point is the VPN server that is installed in the company. Typically, this server is treated as an internal resource of the company, so it is also protected, for example by a firewall. It is not directly exposed to the Internet. This is why cybercriminals usually attack the weakest link, i.e. the user who must somehow connect to this secured VPN server. But not only.
How do criminals disrupt VPNs?
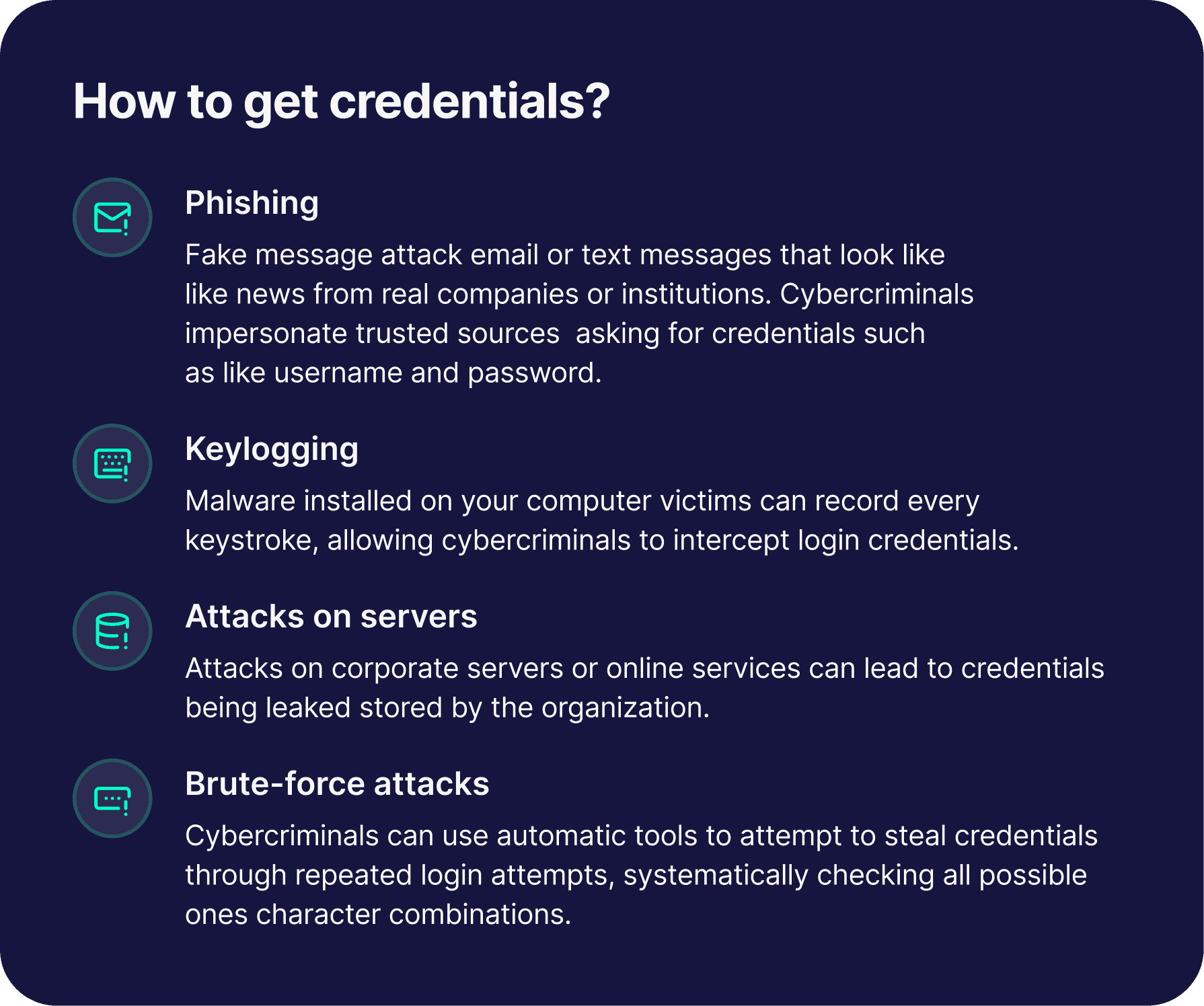
Hijacking of credentials
Attackers most often target the authentication process. Therefore, they are interested in access data, which they can obtain in many ways, including through phishing. If they get their hands on an employee's login and password, they can easily access a secured communication channel with company resources.
DDoS attacks
Criminals also attack the part of the VPN server exposed to the Internet. In this case, they usually burden the network by using DDoS attacks. Distributed Denial-of-Service is a type of cyber attack that aims to prevent access to a service or network device by overloading it with too many false requests.
Weak encryption attacks
Cybercriminals can also break the encryption used by VPNs and thus intercept confidential data transmitted by the user. To do this, they use known vulnerabilities in encryption algorithms or try to guess the encryption key by trial and error. Modern encryption algorithms such as AES-256 are very resistant to this type of activity, but older ones such as PPTP may be vulnerable to attacks.
Zero-day vulnerabilities
Any application that, as a matter of principle, must be exposed to the Internet is vulnerable to zero-day attacks. They exploit vulnerabilities in software that neither software producers nor users are aware of yet.
Authentication bypass attacks
This type of attack, also known as "authentication bypass", involves bypassing the authentication process to gain access to a system or application. There are various methods of bypassing authentication attacks, including exploiting application vulnerabilities, configuration errors, susceptibility to SQL injection attacks or URL manipulation.
Thanks to this, the cybercriminal is able to perform operations on the server that a verified user is authorized to perform, even though he did not use his credentials.
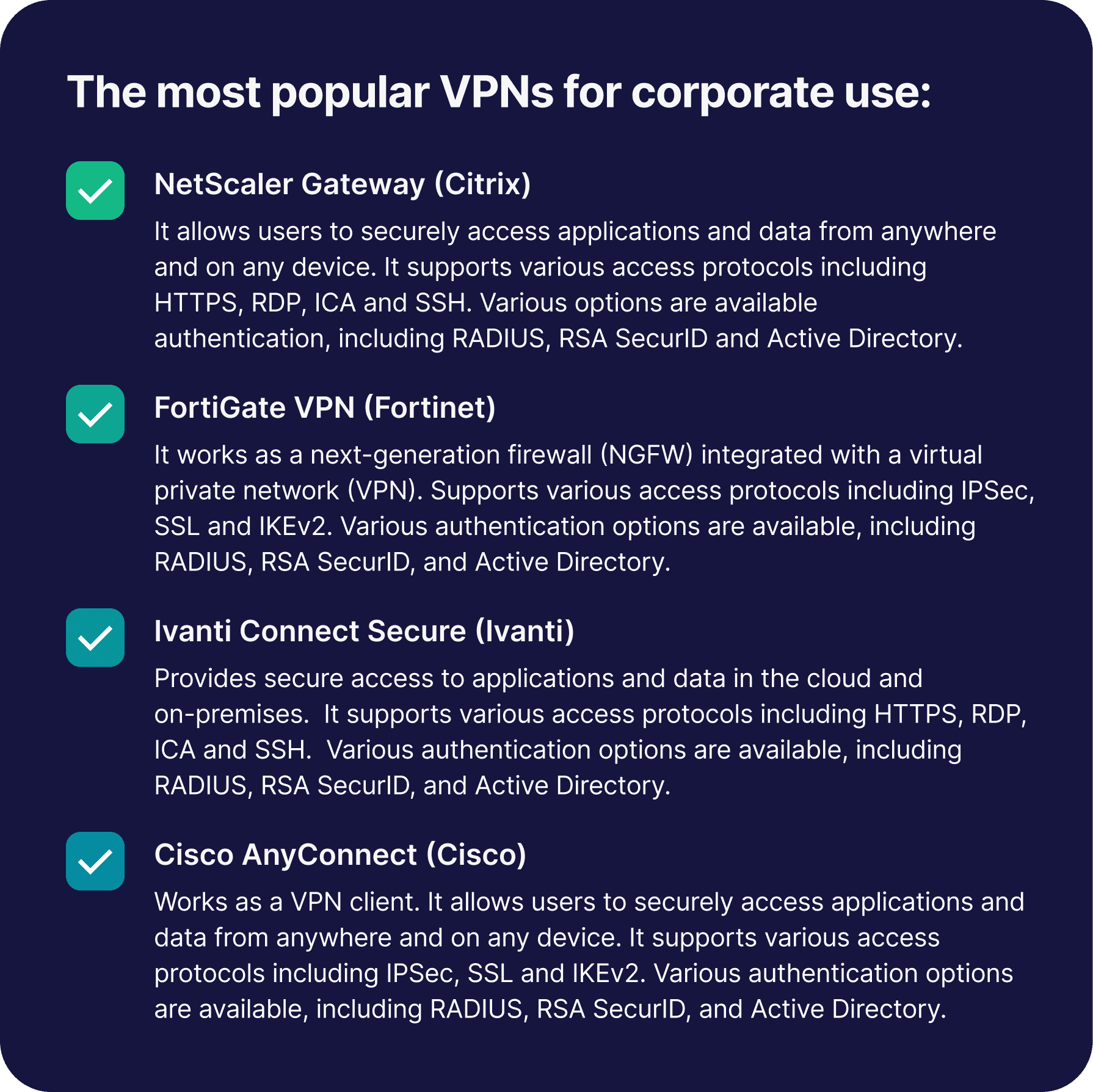
VPN vulnerabilities in practice
Vulnerabilities also occur in the largest and most popular corporate solutions. Only at the turn of 2023 and 2024, two giants, Fortinet
and Ivanti, reported critical vulnerabilities in their systems.
Fortinet warned about a FortiOS security vulnerability that could allow code execution without authentication via a specially crafted HTTP request.
In the case of Ivanti, we were dealing with a combination of two different vulnerabilities that together gave access to the internal resources
of companies using Connect Secure VPN. The first vulnerability was
a vulnerability that allowed an authentication bypass attack to be performed, bypassing authentication. The second one exposed users
to command injection in web components attacks, which involve
an authenticated user injecting any command into another command
that is executed on the server via a website.
Is company data flowing through an encrypted VPN channel safe?
Attacks on a tool that is supposed to ensure the security of company data cause concern. Especially since cybercriminals most often exploit the weakest link, the user. The broadest attack vector on VPN infrastructure
is an authentication attack. Secondly, criminals attack the most common point of contact with VPN, i.e. the website where the VPN login form
is located.
Cybercriminals can obtain user credentials in various ways.
How to strengthen VPN security
How to secure a VPN?
However, enterprises are not helpless in the fight against cybercriminals. They can use additional solutions that will strengthen the security of VPNs and, above all, eliminate the most frequently used attack vectors.
In this case, it will be effective to use strong authentication mechanisms that will not allow criminals to get into the VPN tunnel even if they have the user's credentials. Strong mechanisms include adding a second authentication factor and even completely eliminating passwords that
are easy to hijack or guess.
The second way to secure a VPN is to use the Full Site Protection (FSP) tool, which protects access to the VPN login form page that is often attacked by cybercriminals. Thanks to this solution, the website is not visible on the Internet and therefore becomes inaccessible to third parties.
Implementation of strong authentication mechanisms
Strong authentication is an advanced method of verifying a user's identity in processes related to electronic payments and access to online accounts and services, including VPN servers. It requires at least two independent, difficult-to-forge verification steps. They can use something that the user knows (password), has (phone) or is (biometrics).
Thanks to this, the password and login alone are not sufficient to access the VPN tunnel. The user must confirm his identity, e.g. using a code sent via SMS or his own fingerprint.
Importantly, in solutions of this type it is also possible to completely abandon passwords in favor of passwordless verification. It is believed that the future of authentication is phishing-resistant authentication multi-factor based on biometrics and cryptography, i.e. FIDO.
FIDO Alliance is an association founded in 2013 whose mission is to develop and promote authentication standards that eliminate the use of passwords on websites, applications and devices.
The FIDO Alliance today has over 250 members. They include global technology leaders such as Microsoft, Google and Apple, as well as other global corporations, government agencies, service providers and financial institutions.
Since 2022, Secfense has also been a member of the FIDO Alliance.
Strong authentication from Secfense
The User Access Security Broker solution proposed by Secfense enables, among other things, protection of access to the VPN server login interface using multi-factor authentication (MFA) based on FIDO2
or any other authentication method.
User Access Security Broker from Secfense helps ensure the security
of all people employed in the company, both those working on-site
(in a trusted network) and those working remotely. There are dozens
of multi-factor authentication methods available on the market. User Access Security Broker from Secfense allows you to integrate any method into any web application without expensive programming. Implementing strong authentication with Secfense takes just a few minutes, not weeks or months as with traditional adoption methods.
Full Site Protection
The security of access to the VPN server is also improved by the Full Site Protection solution. This is the operating mode of User Access Security Broker, which guarantees access to the application's web interface only to people with a registered second factor of authentication. People without the second component registered will not even be able to get to the VPN server login page.
The main goal of Full Site Protection by Secfense is to give security administrators full control over the authentication process. With Full Site Protection, authentication from an untrusted network is only possible if the user has previously activated their second authentication factor. Activation of the second component is performed via User Access Security Broker in a trusted network, most often on the company's premises, or via an e-mail activation mechanism. After registering the second component, the user can log in to the application from anywhere, maintaining the same level of security as on a trusted network. For other people, the VPN server login page is invisible.
How Secfense Suite protect popular VPNs
The VPNs most commonly used in companies, such as NetScaler Gateway or Ivanti Secure Access, use the SAML (Security Assertion Markup Language) protocol to enable single sign-on (SSO), which allows users to secure and convenient access to many applications
and services using one set of credentials.
Secfense protects Netscaler Gateway, Ivanti Secure Access and other on-premise applications through integration with UASB, allowing you to add multi-factor authentication (MFA), including phishing-resistant methods such as FIDO, directly to your enterprise infrastructure.
Secfense also protects popular VPNs using Secfense IdP (Secfense Identity Provider) thanks to support for the SAML protocol. In this case, Secfense IdP is used for strong authentication, while UASB and its Full Site Protection functionality for securing login pages exposed to the Internet.
Secfense IdP enables the transition to passwordless, i.e. replacing passwords with convenient and phishing-resistant authentication (FIDO passkeys). It also offers easy integration with various IAM services
and seamless migration between them, which increases flexibility in managing user identities.
How do Secfense solutions improve VPN security?
Secfense IdP
Uses passwordless authentication based on FIDO passkeys.Secfense UASB (User Access Security Broker)
Adds strong, FIDO-based authentication without interfering with the VPN tool code.Secfense Ghost
Make VPN, Citrix, and OWA invisible from the internet.
Secure employee access to the VPN server
If you want your company's data to be safe and your employees to be able to log in to the VPN server without fear of cybercriminals, please contact us.
Share:

Secure Your VPN: How to Protect Company Data from Cyberattacks on VPNs
Mar 14, 2026

Passwordless in Practice: Comparing Enterprise Deployment Architectures
Mar 12, 2026

FIDO Alliance Spotlights Secfense in Passkey Pledge Update
Nov 26, 2025

4 Executive Summaries to Help Security Leaders Justify Cybersecurity Investments
Oct 11, 2025

Secfense Ghost: Taking Exposed Services Off the Map
Sep 22, 2025

Sandis chooses Secfense and secures accounts of thousands of users
Sep 8, 2025

U2F Keys in 2025: Still secure, but FIDO2 and passkeys lead the way
May 11, 2025

Secfense receives U.S. patent for technology enabling passwordless login across organizations
Apr 16, 2025

SALTUS Ubezpieczenia Enhances Security with Secfense’s 2FA Broker
Aug 14, 2024
