Passwordless authentication is often presented as a simple upgrade: replace passwords with passkeys or FIDO2 authenticators and security improves overnight.
In practice, large organizations quickly discover that the real challenge is not the authentication method itself. The challenge is how passwordless authentication is introduced into an existing enterprise architecture.
Legacy systems, vendor applications, strict change management processes, and regulatory requirements fundamentally shape what is technically feasible.
In other words, the difficulty of passwordless deployment rarely comes from the authentication method itself — it comes from the architecture it must fit into.
This article summarizes a technical webinar delivered by Bartek Cieszewski, Solutions Architect at Secfense, exploring how passwordless authentication is actually deployed in enterprise environments and how different architectural models compare.
If you prefer to watch the session, you can also rewatch the full webinar recording at the end of this article.
In Brief
This article explains how organizations deploy passwordless authentication in enterprise environments. It compares five common architectural models:
Native WebAuthn in applications
Gateway-based authentication
LDAP proxy
Agent-based authentication
Reverse proxy authentication
It is intended for:
enterprise architects
IAM leaders
security architects
CISOs
IT teams planning passwordless or passkey rollouts
The core conclusion is simple:
Passwordless is not just an authentication feature. In enterprise environments, it is an architectural program.
Key Definitions
Passwordless authentication
An authentication model that does not require users to enter a password during sign-in.
Passkeys
FIDO2/WebAuthn credentials based on public-key cryptography, typically stored on a device, security key, or managed authenticator.
WebAuthn
A web authentication standard used to enable phishing-resistant authentication with passkeys and FIDO2 authenticators.
FIDO2
A set of standards for passwordless and phishing-resistant authentication using public-key cryptography.
Reverse proxy authentication
An authentication architecture in which a control layer sits in front of applications and enforces access policies before traffic reaches the protected application.
LDAP proxy authentication
A model in which passwordless authentication is translated into LDAP-compatible flows for legacy environments.
Webinar Overview

The session focuses on one key architectural question:
Where should passwordless authentication be introduced in an enterprise environment?
Possible integration points include:
Application layer
Identity layer
Infrastructure layer
Each option leads to different operational consequences.
Why Passwordless Deployment Is Hard in Enterprises
Many passwordless demos show a simplified scenario: a single application, modern web stack, and full development control.
Real enterprise environments look very different.
Organizations typically operate with:
hundreds of applications
shared identity infrastructure (AD, LDAP, SSO)
mixed authentication protocols (HTTP, LDAP, thick clients)
legacy technologies such as NTLM
strict change control and audit requirements

In such environments, passwordless authentication is not simply a feature rollout.
It becomes an architectural transformation program.
The First Architectural Question
Where Do You Attach Passwordless?
Before evaluating vendors or technologies, architects must answer a fundamental question:
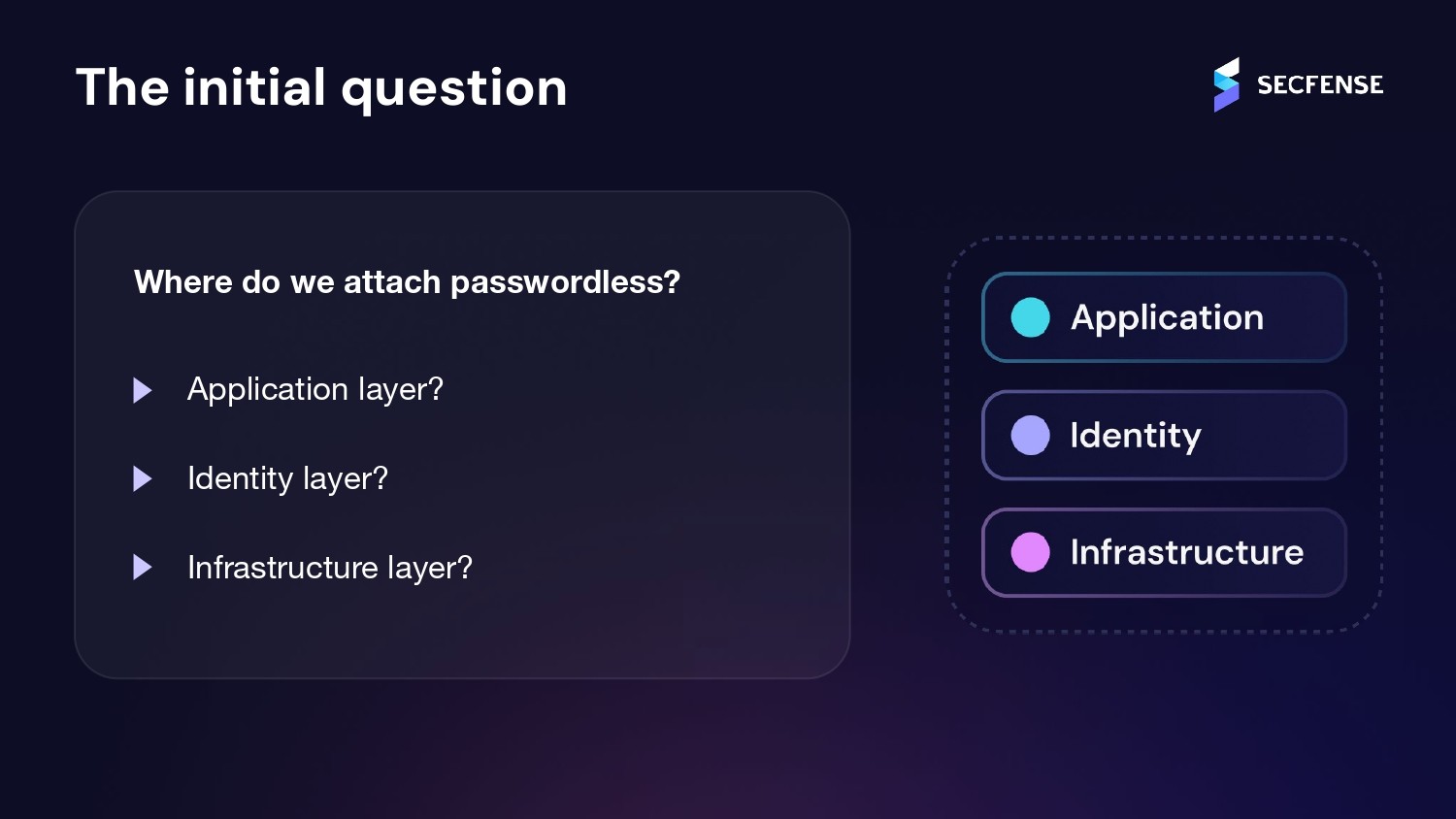
At which layer of the architecture should passwordless authentication be introduced?
Typical integration points include:
Application layer — authentication implemented directly in application code
Identity layer — authentication enforced by IAM platforms
Infrastructure layer — authentication enforced before traffic reaches the application
This decision determines:
deployment complexity
long-term maintenance
compliance visibility
migration flexibility
Five Common Passwordless Deployment Architectures
Enterprise deployments typically fall into five architectural patterns.

The webinar compares these models based on four criteria:
required application changes
scalability
compliance visibility
migration flexibility
1. Native WebAuthn in Applications
What It Is
In this model, WebAuthn is implemented directly in application code.
Typical scenarios include:
new web applications
SaaS platforms
greenfield development projects
This is often considered the cleanest architecture from a design perspective.
Advantages
clean architecture
full control over user experience
no additional infrastructure required
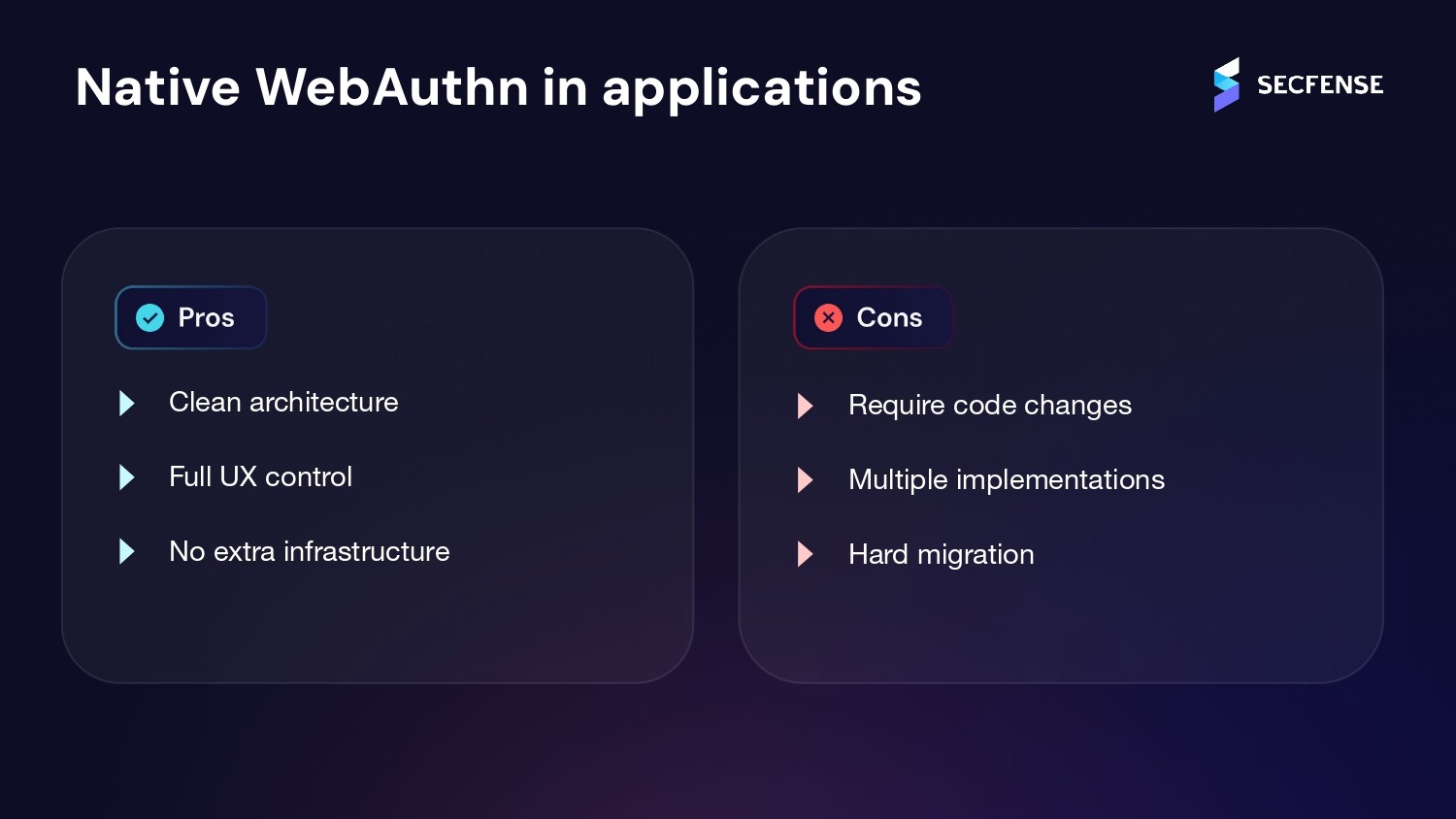
Limitations in Enterprise Environments
However, native WebAuthn deployments quickly become difficult to manage at scale.
Key challenges include:
Every application becomes a separate implementation
Each application requires:
development
testing
documentation
maintenance
Code changes are required
Many enterprise applications:
are vendor-managed
cannot be modified
require lengthy certification processes
Migration is usually binary
Users must either:
fully switch to passwordless
or continue using passwords.
This makes gradual rollout significantly harder.
2. Gateway-Based Authentication
What It Is
This model introduces a central authentication gateway, typically integrated with IAM or SSO platforms.
Typical environments include:
organizations with a dominant IAM platform
environments already standardized around SSO
centralized web application access
Advantages
centralized policy enforcement
integration with existing IAM systems
Limitations
Despite the centralization benefits, gateway deployments introduce constraints:
application-side integration is often required
flexibility is limited
migration options may be restricted
In legacy environments, modifying applications to fit the gateway model may not be feasible.
3. LDAP Proxy Model
What It Is
This architecture translates passwordless authentication into LDAP bind operations, allowing legacy applications to continue using existing LDAP authentication flows.
Typical use cases include:
Active Directory or LDAP-centric environments
older enterprise stacks
systems relying heavily on LDAP authentication
Advantages
no application changes required
fast deployment in LDAP-centric environments
Limitations
However, LDAP proxies have important architectural constraints:
limited MFA capabilities
potential compliance gaps
difficulty supporting full FIDO2 authentication
They work best as transitional solutions rather than long-term passwordless architectures.
4. Agent-Based Authentication
What It Is
Agent-based architectures install authentication agents on endpoints or servers.
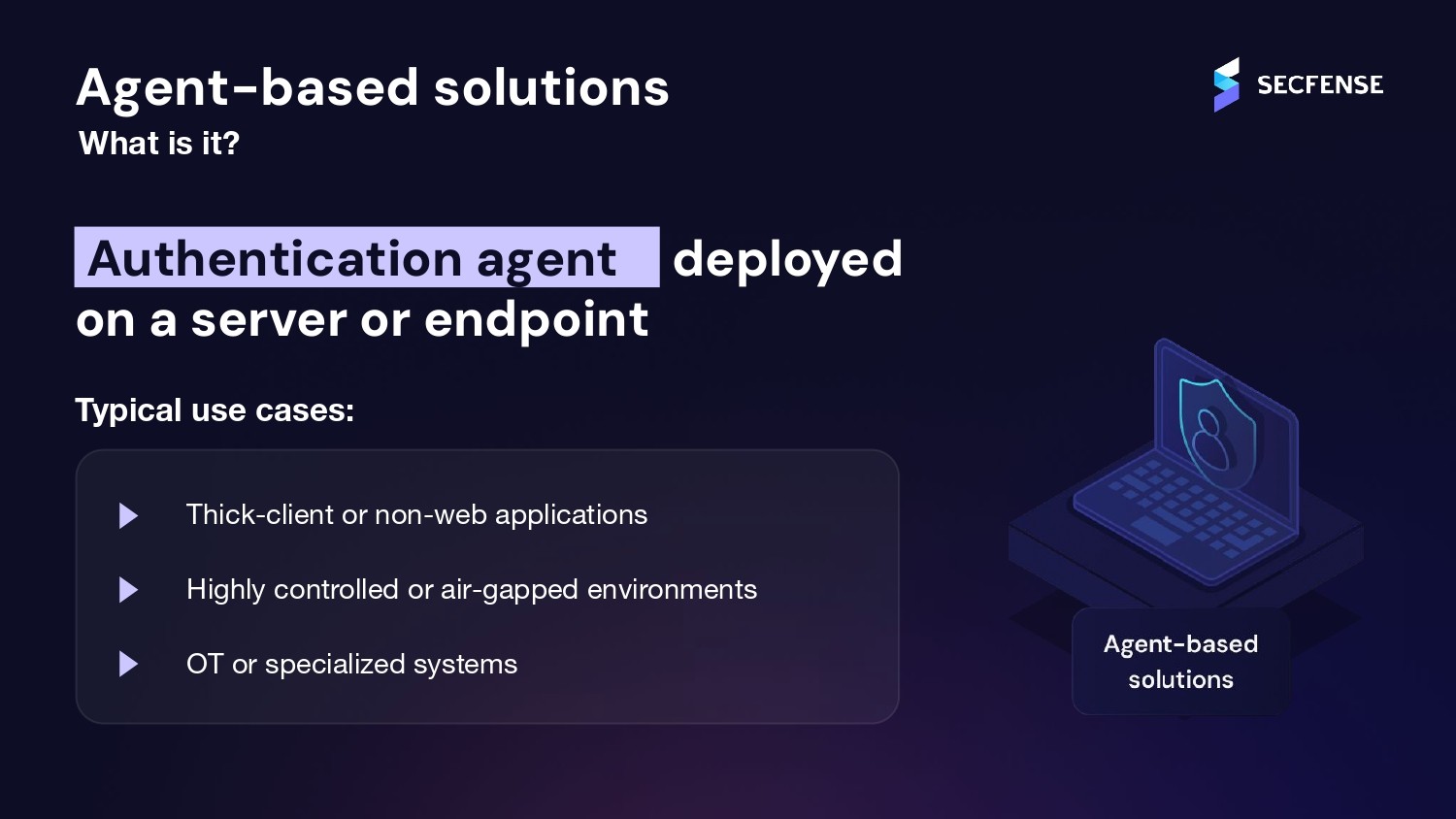
Typical environments include:
thick-client applications
air-gapped environments
OT or specialized systems
Advantages
deep integration with workloads
strong control over authentication flows
Limitations
The main trade-off is operational complexity.
Agent-based systems introduce:
lifecycle management
compatibility issues
upgrade requirements
long-term operational overhead
Organizations must clearly define which team owns agent maintenance over time.
5. Reverse Proxy Authentication Model
What It Is
The reverse proxy approach introduces an authentication layer in front of applications, without modifying application code.
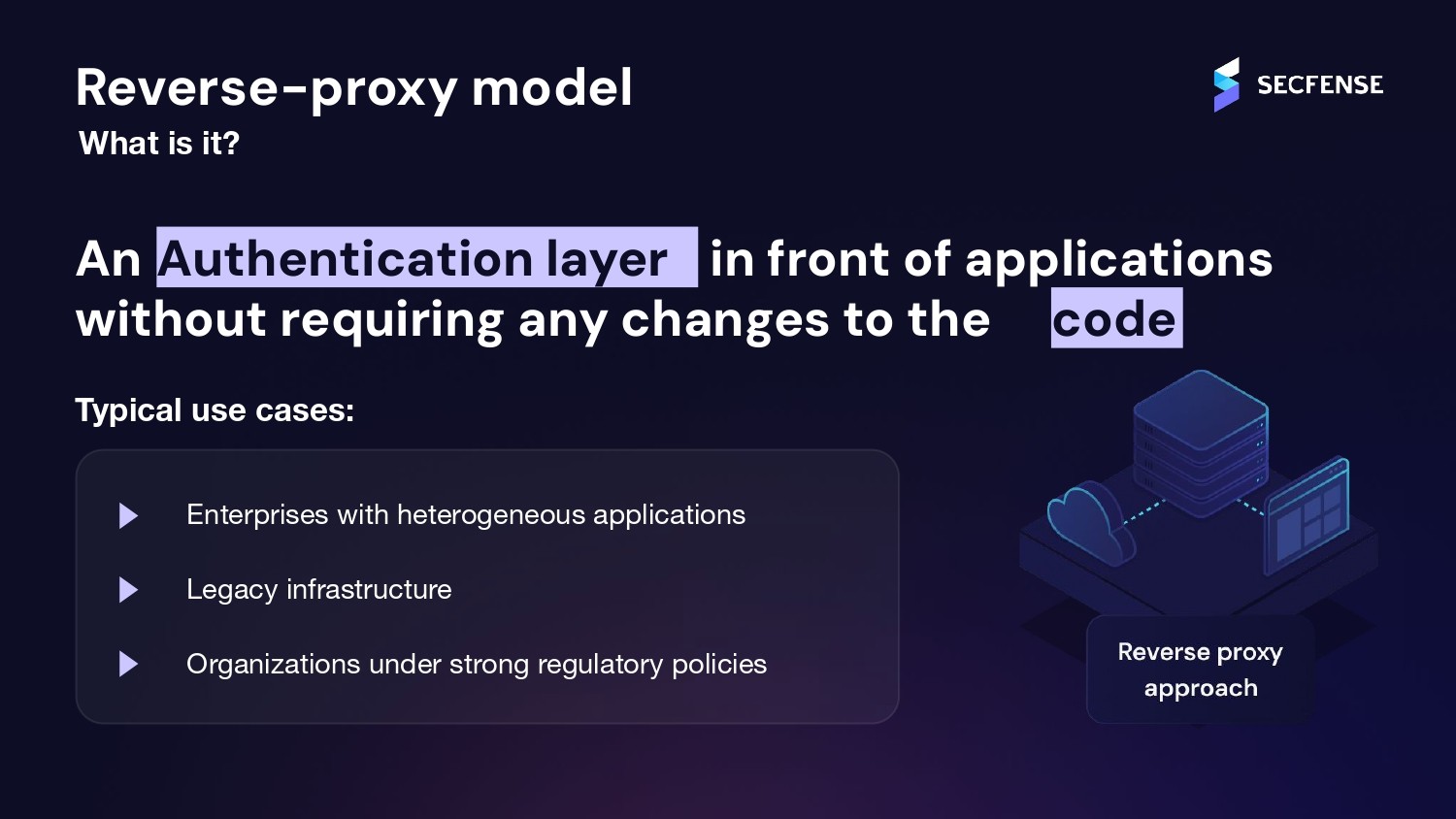
Typical environments include:
heterogeneous application landscapes
legacy infrastructure
regulated industries with strict change policies
Advantages
zero application code changes
centralized policy enforcement
support for gradual migration
strong alignment with compliance requirements
Limitations
The primary trade-off is infrastructure complexity.
Reverse proxy deployments require:
additional infrastructure components
high availability design
In practice, this model often provides the highest flexibility in complex enterprise environments.
Architectural Comparison

Key Architectural Questions Organizations Must Answer
Choosing a passwordless architecture is not primarily a technology decision.
It is an architectural strategy decision.
Security and IAM teams should evaluate several critical questions.
1. Where Are the Integration Points?
Authentication can be introduced at:
the application layer
the identity layer
the infrastructure layer
2. Which Applications Are in Scope?
Enterprises must categorize applications such as:
web applications
legacy systems
vendor-managed applications
thick clients
internal tools
3. Who Owns the Application Code?
If applications are:
internally developed → native WebAuthn may be possible
vendor-managed → code modification may be impossible
4. Can Migration Be Gradual?
Organizations typically require:
pilot programs
early adopters
phased rollouts
Some architectures support gradual migration better than others.
5. What Will Auditors Ask?
Security and compliance teams will ask questions such as:
Where is authentication enforced?
Where are policies defined?
Are logs centralized?
Who maintains the solution?
Why Passwordless Is an Architectural Program
Passwordless authentication is often misunderstood.
It is not simply a feature upgrade.
It is a multi-year architectural transformation.
Organizations differ significantly in:
architecture
regulatory constraints
legacy footprint
application ownership models
Because of this diversity, there is no single universal deployment approach.
The correct architecture depends primarily on the environment you start with.
Different organizations will reach different conclusions based on their architecture, application ownership model, and regulatory constraints.
Secfense Approach to Passwordless Deployment
The Secfense platform was designed around one assumption:
Most enterprise applications cannot be modified.
Common constraints include:
vendor restrictions
risk associated with application changes
regulatory approval processes
For this reason, Secfense focuses on no-code deployment models.
The platform operates at the reverse proxy layer, allowing organizations to introduce:
MFA
FIDO2 authentication
passkeys
without modifying protected applications.
Key design principles include:
no application changes
centralized policy enforcement
compatibility with heterogeneous environments
gradual user migration
centralized audit logging
Passkeys, Authenticators, and Compliance Considerations
Beyond architecture, organizations must evaluate how passkeys are stored and managed.
Common authenticator options include:
hardware security keys
platform authenticators (Windows Hello, Apple, Android)
mobile passkeys
enterprise-managed authenticators
A key consideration is where private keys are stored.
Many platform authenticators synchronize passkeys through vendor cloud ecosystems.
While acceptable in many environments, some regulated industries require:
device-bound keys
hardware-backed authenticators
restricted authenticator types
Architectures can enforce these requirements using attestation policies.
Passwordless Migration Strategies
Organizations rarely move their entire user base to passwordless at once.
Typical rollout phases include:
pilot users
administrator accounts
early adopter groups
wider employee rollout
external users
Architectures that support gradual migration significantly reduce operational risk.
Final Takeaways
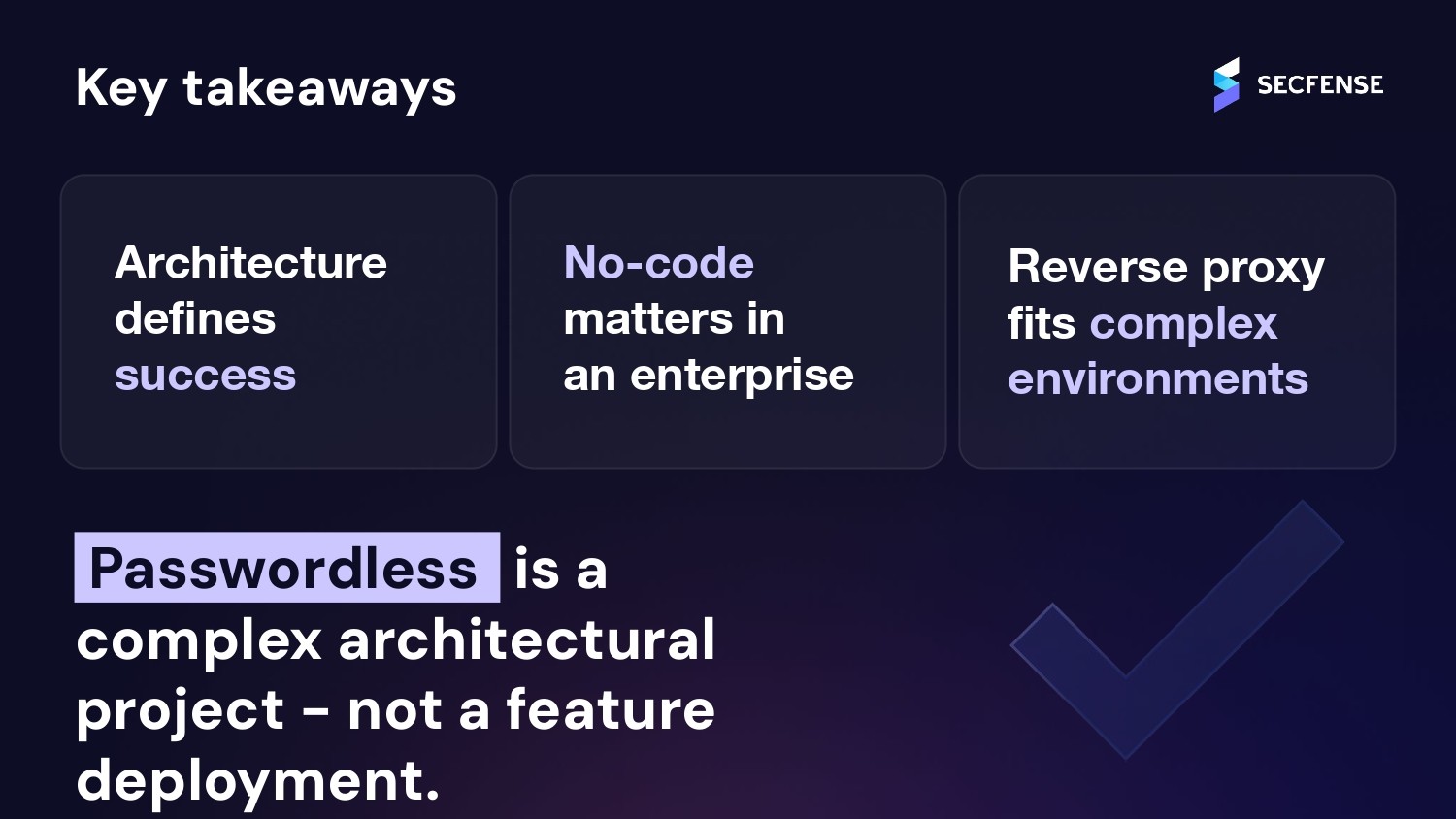
The webinar concludes with several important lessons.
Architecture defines success
Passwordless adoption depends more on integration architecture than on authentication technology.
No-code approaches reduce deployment risk
Avoiding application modifications simplifies enterprise rollouts.
Reverse proxy models fit heterogeneous environments
They provide flexibility across legacy and modern systems.
Passwordless is not a feature rollout
It is an enterprise architecture program requiring long-term planning.
Watch the Webinar Recording
If you would like to explore the topic in more depth, you can watch the full session:
Passwordless in Practice: Comparing Enterprise Deployment Architectures
Learn More About Enterprise Passwordless
If your organization is evaluating passwordless authentication or passkeys for enterprise environments, Secfense provides resources covering:
enterprise passkey architectures
passwordless deployment strategies
compliance and regulatory considerations
integration with legacy IAM environments
FAQ: Enterprise Passwordless Deployment Architectures
What is the main challenge of deploying passwordless authentication in enterprises?
The main challenge is not the authentication method itself, but introducing passwordless into complex environments with legacy systems, shared identity infrastructure, and strict change management.
What are the main enterprise passwordless deployment models?
Common deployment models include:
native WebAuthn in applications
gateway-based authentication
LDAP proxy
agent-based solutions
reverse proxy authentication
When does native WebAuthn make the most sense?
Native WebAuthn works best for new applications, greenfield projects, and environments where the organization owns the application code.
Why is reverse proxy often attractive in enterprise environments?
It allows organizations to introduce passwordless authentication without modifying application code while maintaining centralized policy enforcement and supporting gradual migration.
Is LDAP proxy enough for full passwordless adoption?
LDAP proxy can work well in AD-centric environments but often has limitations around MFA flexibility and full FIDO2 support.
Can passwordless be rolled out gradually?
Yes. However, not every architecture supports gradual rollout equally well. Reverse proxy architectures typically provide stronger migration flexibility.
What should auditors and compliance teams ask during a passwordless project?
Common questions include:
where authentication is enforced
where policies are defined
whether logs are centralized
who owns operational maintenance
Is passwordless a feature or an architectural program?
Passwordless authentication should be treated as an architectural transformation program rather than a simple feature deployment.
Share:

Secure Your VPN: How to Protect Company Data from Cyberattacks on VPNs
Mar 14, 2026

Passwordless in Practice: Comparing Enterprise Deployment Architectures
Mar 12, 2026

FIDO Alliance Spotlights Secfense in Passkey Pledge Update
Nov 26, 2025

4 Executive Summaries to Help Security Leaders Justify Cybersecurity Investments
Oct 11, 2025

Secfense Ghost: Taking Exposed Services Off the Map
Sep 22, 2025

Sandis chooses Secfense and secures accounts of thousands of users
Sep 8, 2025

U2F Keys in 2025: Still secure, but FIDO2 and passkeys lead the way
May 11, 2025

Secfense receives U.S. patent for technology enabling passwordless login across organizations
Apr 16, 2025

SALTUS Ubezpieczenia Enhances Security with Secfense’s 2FA Broker
Aug 14, 2024