The MFA is better than the password itself. That’s for sure. However, the MFA itself has long since lost its sense of security. Traditional methods like SMS and TOTP can already be easily cheated, and in this article, we will deal with this very topic.
Trickery and Technology: the Attack Scheme
Let’s imagine a scenario where a cybercriminal wants to take over a Microsoft 365 account. He starts by creating a convincing imitation of a legitimate domain and then, using social engineering, convinces the user to click on the infected link contained in the e-mail. The user clicks on a legitimate-looking link without knowing that “Evilginx” has already started running in the background.
Evilginx Tool: Phishing at a Higher Level.
Evilginx is a malicious man-in-the-middle tool that allows criminals to intercept credentials and authentication tokens, thus bypassing multi-factor authentication (MFA). The process begins by cloning the Evilginx repository and preparing a suitable environment to launch the attack, whether on Linux or Windows.
Configuring the Attack Environment
Criminals set up a phishing server, using services like Digital Ocean to create a credible-looking fake website. The goal is to get a potential victim to provide their login information unknowingly.
Phislets: The Key to Successful Phishing
Phislets are configuration scripts used by Evilginx to target specific websites. Creating a phislet requires knowing the site’s structure under attack and adjusting variables such as proxy hosts, authorization tokens, and user credentials accordingly.
Live Attack Using Evilginx
On his YouTube channel, John Hammond recently demonstrated how to launch a phishing attack on a Microsoft 365 account using Evilginx. The video shows modifying YAML files, configuring a domain, and using a reverse proxy to trick login credentials.
Social Engineering in Action
The social engineering aspect of phishing attacks is as crucial as the hacking tools and techniques. Using manipulative skills, criminals target people’s natural inclinations and reflexes, such as trust, fear, or urgency to act, to elicit an automatic, reckless response. By creating the illusion of authenticity, such as impersonating official communications from well-known companies or institutions, they force victims to disclose their data in a process that, at first glance, appears to be a standard verification procedure. Social engineering enables criminals to pass through two-factor security, where the second factor – the person and his tendencies – is the weakest link. Criminals are not only successful in phishing for authentication information through psychological techniques. Still, they can install malware on victims’ devices or access sensitive resources, using them to further fraud or sell them on the black market, ultimately taking complete control of compromised accounts.
Assumption of Full Entitlement
Once digital criminals gain access to login credentials, the opportunity to escalate privileges up to the administrator level opens up a particularly dangerous dimension of cyberattacks. With full administrative privileges, they can not only freely roam network resources, manipulate data, and create or delete user accounts but also implement backdoors that will ensure long-term access to the system even after the original entry point is detected and removed. Such action threatens immediate business continuity and poses the risk of leaking sensitive data, including the personal information of customers and employees, which can lead to significant financial and reputational losses for the organization. The attacker’s assumption of full privileges transforms the initial phishing attack into a persistent and complex threat that requires much more difficult and costly intervention to restore the security and integrity of IT systems.
How to Defend Against Evilginx and MFA Workarounds
The development of tools such as Evilginx2 underscores the evolution of phishing techniques that are becoming increasingly sophisticated, using man-in-the-middle (MitM) attacks to steal login credentials and two-factor authentication tokens. The use of such tools by attackers poses a significant threat to organizations’ cyber security worldwide. However, as pointed out during the discussion led by Adam Haertle (Trusted Third Party), there are methods and tools to counter such threats effectively.
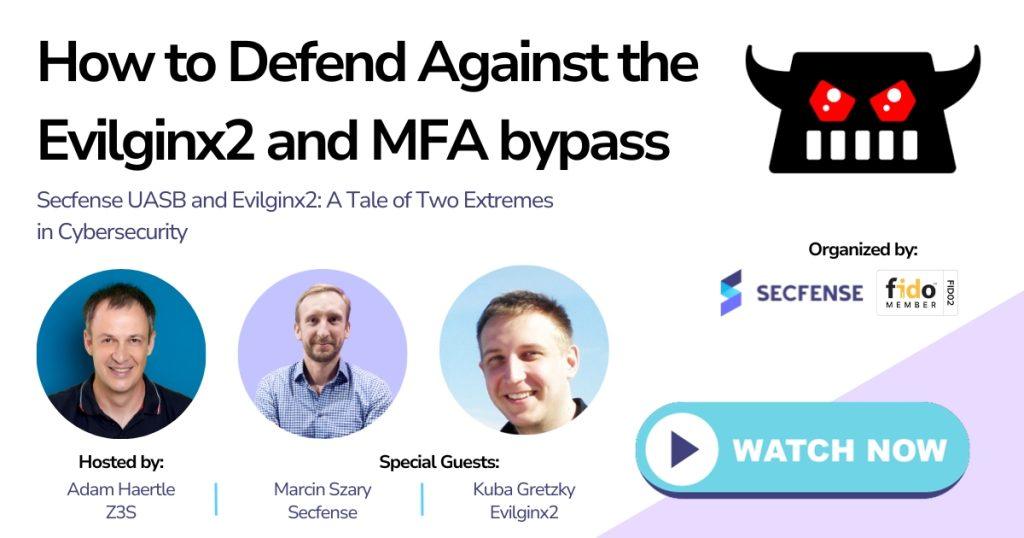
An essential part of the defense against attacks using Evilginx2 is the Secfense User Access Security Broker (UASB), developed by Marcin Szary, CTO and co-founder of Secfense. This solution makes it possible to implement strong authentication (e.g., FIDO2, passkeys) on a large scale without modifying existing applications or infrastructure. The webinar, which also featured Evilginx2 solution developer Kuba Gretzky, addressed the effectiveness of FIDO authentication in countering such threats and discussed how Secfense UASB facilitates FIDO implementation by eliminating the need to write code.
Suppose you want to explore the technical nuances of Evilginx2’s performance and understand how Secfense UASB can enhance your organization’s defense strategy. In that case, we encourage you to register and watch the transcript of a discussion with the developers of these two technologies. This is a unique opportunity to learn practical strategies for implementing FIDO authentication and better understand the limitations of traditional MFA and methods for overcoming them.
In addition to gaining expert knowledge, the webinar is a chance to understand how the contrasting ends of the cyber security spectrum – attackers and defenders – can shape the future of online security.
